Many of us have either experienced issues with our own website security or heard about other companies and their cybersecurity problems. The importance of digital security is a lesson that far too many businesses learn the hard way. Ashley Madison, the “dating” site designed to hook up people for extra-marital affairs, reported that its user data was stolen last August. That led to some sleepless nights for more than a few cheating spouses and almost certainly helped line the pockets of several divorce attorneys.
Shortly thereafter, the U.S. federal government’s Office of Personnel Management (OPM) reported that it was hacked as well. To make matters worse, the personally identifiable information (PII) of government employees and contractors was stolen, leading to the possibility of identity theft. The government attempted to compensate for the problem by signing up more than 21 million people for free credit monitoring.
It’s not just websites that promote adultery and government databases that have been hacked, either. In fairly recent history, Home Depot, Target, and Sony have all felt the sting of hackers.
If it can happen to them, it can happen to you.
That’s why you need to take your website and data security seriously. It’s not enough just to add password protection and hope that your service provider takes care of the rest. You need to be vigilant, anticipate the threat of hackers, and make it as difficult as possible for unauthorized people to access your site.
I speak from experience. I’ve seen sites hacked many times.
And I can tell you this: cleaning it up is a hassle.
It’s much easier to prevent attacks than it is to fix the damage caused by hackers after you’ve been the victim of a security breach. An ounce of prevention is definitely worth a pound of cure here.
In this article, we’ll show you how to implement state-of-the security measure to minimize the risk of a hacker wreaking mayhem with your data (or, worse yet, your customer’s data). Specifically, we’ll look at ways to protect your WordPress website from hackers.
Security Plugins
Fortunately, there are plenty of plugins to help you protect your WordPress website.
One of those plugins is called WordFence. As of this writing, it has more than 1 million downloads from the WordPress website and enjoys an outstanding 4.9/5 rating.
Even better: WordFence is free.

There’s a caveat to that, though. Like many other WordPress plugins, you get the “basic” tool for free. However, if you want advanced features, you’ll have to fork over some cash. How much you spend depends on the number of sites you need to protect and the length of your plan. The company is offering an assurance that users won’t have to spend more than $4.92 per month per site.
The basic plan offers a free scan and will alert you if your site gets compromised. It also provides you with a live traffic view so you can see if people are trying to hack your site.
The premium plan offers additional bells and whistles such as country blocking, password auditing, and scheduled scans. You also get premium support in the event that you need to talk to a human being about the software.
Another plugin, iThemes Security, also helps you protect your site. It’s been downloaded more than 700,000 times and has a 4.7/5 rating.
iThemes Security is an excellent option for webmasters who “don’t know what they don’t know.” The plugin looks for security holes and patches them. It also offers enhanced authentication and stops automated attacks.
As with WordFence, iThemes Security is free but offers a premium plan, called iThemes Security Pro. The price on the premium plans range from $80-$247 per year, depending on how many sites you need to protect and whether or not you need developer licensing.
Security Tools
Some security tools are offered independent of WordPress. That is, you can use them whether or not you’re running a WordPress site.
One tool, Sitelock, offers a rich feature set of data security that should keep the barbarians away from your gate. The company offers several plans, each with various pricing models. Unfortunately, you’re going to need to call the company to get a quote based on the data security needs of your site.

The basic plan offers daily vulnerability scans, malware removal, denial-of-service protection, and sets up a firewall for your site. Other plans include additional security measures: SQL injection prevention, XSS injection prevention, vulnerability repair, and blocked access to back-door files used by hackers.
Keep in mind that if you want to go with SiteLock, it’s recommended that you give them File Transfer Protocol (FTP) access to your site so that they can scan your site periodically for malware.
You should also have a look at Incapsula and CloudFlare. They both provide firewall services and prevent bad bots from crawling your site. Additionally, they prevent SQL injections and even offer content delivery networks (CDNs) that speed up your website.
On a personal note, I use Incapsula and can’t recommend it highly enough.
Also, if you’re particularly interested in malware protection, have a look at Sucuri. This company offers a free site scanner that will check your site for malware, errors, and out-of-date software.
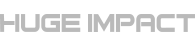
Google Search Console
Thus far, the tools we’ve looked at (at least the premium versions) come with a price tag. However, there’s one great tool that will help you with site security that’s offered completely free of charge. In fact, you’re probably already using it: Google Search Console.
To check security on your site using the Search Console, just login to it like you normally do. Then, on the bottom of the left-hand sidebar, you should see an item labeled “Security Issues”. Click on that and Google will give you a rundown of everything that’s wrong with your site from a security perspective. The tool will also offer advice about how to fix the security issues that it finds.
Keep in mind that the Search Console shouldn’t be viewed as a robust tool to lock down your site. Instead, you should use it in addition to other security measures.
Best-Practices to Keep Your Site Secure
In addition to the tools mentioned above, you can help keep your site secure by following a few “best-practices” that make it more difficult for hackers to gain access.
For starters, you should change the login URL from the default. Almost every hacker in the world knows that the configured URL to login to a WordPress site is the domain name of the site followed by “/wp-admin”. With that knowledge, they can attempt “brute force” attacks (basically, they just keep trying to guess the password over and over again) until they finally get in. Instead of making it easy for those hackers, use a plugin to rename the login URL. It’s worth noting that the iThemes security solution mentioned above also lets you change the admin URL.
Also, be sure to pick long passwords that are hard to guess. You might get frustrated when you’re registering on a website and it tells you a bunch of rules that you have to follow for your password. The reality is that those kinds of rules exist not only for your own protection, but also for the protection of the website itself. Use password generators that create cryptic passwords that include a combination of upper- and lower-case letters, numbers, and symbols. Those are usually much harder to guess than the names of your children.
I use LastPass to manage all my passwords. It not only generates secure passwords for each site, it also ensures that every site has a unique password. On top of that, it stores my passwords securely in its own database. All I have to do is remember one master password, and I’m all set to login to any site where I’m registered.

Keep your software up to date as well. That includes not only the WordPress installation itself, but also the plugins and themes. If you’d like to automate the process of keeping your WordPress software up to date, install the Advanced Automatic Updates plugin.
It was reported last year that hackers took advantage of the vulnerabilities in a couple of WordPress plugins. Those vulnerabilities were resolved with subsequent updates. Webmasters who didn’t update the plugins are still susceptible to attacks. That’s why it’s important to keep your software updated.
If you’re familiar with PHP and WordPress software, you can force auto-updates to the core installation by adding one simple line to a file. Just open wp-config.php and add this line (if it doesn’t already exist):
define ( 'WP_AUTO_UPDATE_CORE', true );While we’re on the subject of plugins and their vulnerabilities, it’s important to know that one of the best (and easiest) things you can do to limit the potential for an attack is to also limit the number of plugins that you use. If you’ve got a bunch of plugins on your site that are still active and you’re certain that you’re not using them anymore, deactivate and uninstall them. Hackers can’t exploit vulnerabilities that don’t exist.
Also, pick the right plugins. These days, it seems like everybody with a basic knowledge of PHP and WordPress is producing a free plugin and uploading it to WordPress.com. If you see a plugin that looks like it has a feature set perfect for your site, check the number of downloads. Be wary about installing anything with less than 100,000 downloads and/or a sub-par rating. You don’t want to be somebody else’s beta-tester, especially when it comes to security. Keep in mind, though, that the 100,000 number is a general rule (that I even break on occasion). When you’re evaluating any plugin, be sure to take everything into account, including the rating, the developer’s reputation, and compatibility with the latest WordPress version.
Finally, you should also disable admin access directly to files in your WordPress installation. That way, hackers who manage to get into the WordPress back end won’t be able to edit files directly. The easiest way to disable the admin access to files is to add the following line to your wp-config.php file:
define ( 'DISALLOW_FILE_EDIT', true );Server Side Security
Although you can do a lot between plugins and best-practices to make security a priority, there’s also a lot that you can’t do because you don’t own the hardware infrastructure or manage the network where your site is hosted. That’s why it’s important that you pick a hosting provider that takes security seriously.
While it might be tempting to select a hosting provider on the basis of cost alone (especially if you’re running a struggling startup), you’re going to have to look at more than just the monthly price if you want your site to be secure. Get feedback from other people you know about the hosting solutions that they’re using. Ask them if they’ve experienced any security issues and why. Specifically: ask them if they get emails from time to time from their providers letting them know about a hack attempt that was thwarted. That’s a good indication that the company is proactive in preventing security breaches.
Use Secure Sockets Layer (SSL) as well to provide an additional layer of security. If you’re unfamiliar with SSL, it’s an encryption format that protects data transferred between a browser and the server. If any “prying eyes” intercept encrypted SSL data sent to or from the server, all they’ll see is what appears to be garbage instead of sensitive information.
To use SSL on your own WordPress site, you can try to set it up yourself. However, it’s probably best to get a professional involved. It’s too easy to “break” something by making a mistake.
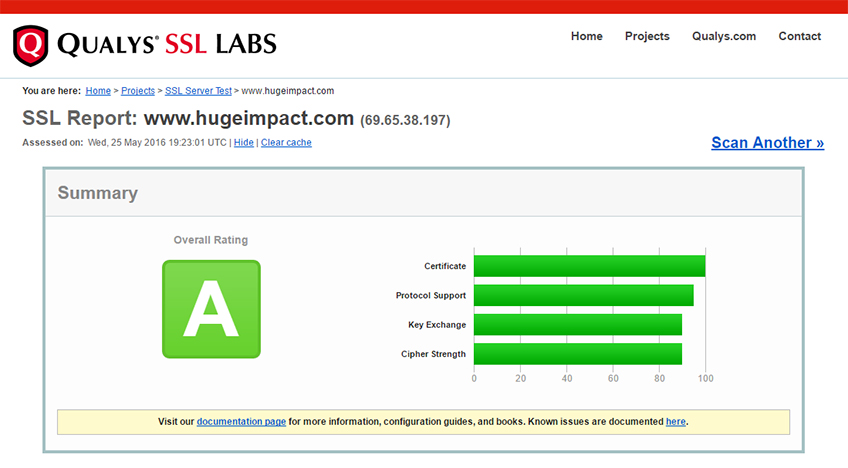
Once you’ve implemented SSL, you can test it out with the SSL Labs Server Test. That tool will also let you know if your host is secure and report back any vulnerabilities on the server.
Also, don’t forget to secure your database as well. All WordPress installations have a MySQL database that’s used to store posts, pages, and information about images. Be absolutely certain that the admin account for your database has a cryptic password and that the user name isn’t something obvious (like “admin”).
If your hosting provider is using a UNIX platform (a likely scenario), you should also secure the files that your site is using. You can do that because the various flavors of UNIX allow you to grant read, write, and executable access to specific directories and files. Follow this guide or, better yet, talk to a professional administrator about granting the right access to your important WordPress files. You don’t want to assign “777” access to your WordPress directories. That will give the whole world write access to the files in those directories, making it easier for hackers to cause problems.
If you need to transfer files to and from your hosting server, make sure that you do so with a secure connection. If you use the plain old File Transfer Protocol (FTP), your name and password is transferred in clear text over the wired (or wireless) connection. Hackers who are monitoring your communications can get your credentials and login to your site with full control.
Instead of using FTP to move files around, consider using the File Manager that your hosting provider almost certainly offers. It should use SSL to encrypt your communications.
If your hosting provider doesn’t offer a File Manager or you want to use your FTP client, make sure it’s a secure solution. Instead of using FTP, use SFTP (SSH File Transfer Protocol) so that your communications are private. WinSCP and FileZilla are both excellent SFTP solutions that also have the benefit of being free.
Also, if your hosting provider is using cPanel, you should check the “Security” section of your cPanel console for various solutions. One solution, cPHulk, protects your site from brute force attacks. ConfigServer Security & Firewall is also useful for intrusion detection and offers cPanel integration.
User Security
It may be the case that you’re running a WordPress installation with multiple users. If so, you have an added layer of security that you need to cover.
Begin by ensuring that each user has the appropriate access. It’s not likely that all of your users need Admin access. People who are contributing content to your site should have Author access. Editors, who make the decision on whether or not to publish certain pieces, should have Editor access. Also, be sure to remove old, inactive users.
You’ll also want to limit the number of users on your system as much as possible. If you’re allowing people to create accounts so that they can leave comments on your site, consider ditching the native commenting feature of WordPress and opting for a third-party solution, such as Disqus or, better yet, Facebook Comments.
You should also implement two-factor authentication for your users. It’s called “two-factor” because it uses two forms of credentials instead of just one. The first security measure is the traditional name/password pair. The second involves another means of identifying the user, such a security token. The aforementioned WordFence security plugin has a two-factor authentication feature.
Additionally, WordFence can limit the number of consecutive failed login attempts. That will guard your site against brute-force attacks.
Also, use CAPTCHA technology to minimize threats posed by bots attempting brute force attacks. CAPTCHA fields are those little boxes that ask you to prove your humanity by filling out a field with characters presented in an image. It’s much more difficult (although not impossible) for bots to recognize those characters and complete the form.
Fortunately, CAPTCHA plugins exists to help you lock down your site with a CAPTCHA field. Most CAPTCHA plugins can be used for login, registration, password recovery and comment forms.

Along the lines of keeping bots out, you can also use the Contact Form 7 Honeypot plugin if you’re already using the Contact 7 Form for feedback and/or registration purposes. That plugin doesn’t use CAPTCHA technology, but instead creates a hidden field that only bots will fill out when they complete the form. If that field is filled out, the form won’t be submitted.
As with your own password, user passwords should be cryptic and difficult to guess. If your users complain about the complexity of their passwords and how difficult they are to remember, point them to a service like the aforementioned LastPass.com. Good security begins with non-intuitive credentials.
Finally, avoid using default user names (like “admin”). Instead, make user names something more difficult to guess.
On Your Local Machine
Good security doesn’t just involve your remote host. You need to secure the PC that you use for day-to-day work as well.
For starters, make sure that you have quality malware and virus protection software installed on your PC and that it’s updated automatically. Remember, hackers are always finding new ways to break into systems and writing new software that’s used to exploit vulnerabilities. That’s why your anti-virus software must be updated constantly.
Also, install a firewall on your PC. That will make it just a little more challenging for hackers to gain access to your system.
Be sure to password-protect access to your system as well. In the event that somebody steals or gains access to your PC, the system will still be inaccessible to anyone who doesn’t know the password.
Finally, be sure to keep your PC in a location that’s secure. If it’s a laptop, take it with you as much as possible. If it’s a desktop, be sure that your office door is locked.
Wrapping It Up
Bad guys are out there. Sadly, many of them are smart and know how to hack into websites to wreak havoc, steal data, and jeopardize your relationship with your customers. That’s why it’s important that you do everything you can to fully protect your WordPress website. With the help of your hosting provider, a few plugins, and some best-practices, you can go a long way to mitigate the risk of a security breach.